Same thing with SHA-1, 2, and I'm not sure about 3.
linuxmemes
Hint: :q!
Sister communities:
Community rules (click to expand)
1. Follow the site-wide rules
- Instance-wide TOS: https://legal.lemmy.world/tos/
- Lemmy code of conduct: https://join-lemmy.org/docs/code_of_conduct.html
2. Be civil
- Understand the difference between a joke and an insult.
- Do not harrass or attack members of the community for any reason.
- Leave remarks of "peasantry" to the PCMR community. If you dislike an OS/service/application, attack the thing you dislike, not the individuals who use it. Some people may not have a choice.
- Bigotry will not be tolerated.
- These rules are somewhat loosened when the subject is a public figure. Still, do not attack their person or incite harrassment.
3. Post Linux-related content
- Including Unix and BSD.
- Non-Linux content is acceptable as long as it makes a reference to Linux. For example, the poorly made mockery of
sudoin Windows. - No porn. Even if you watch it on a Linux machine.
4. No recent reposts
- Everybody uses Arch btw, can't quit Vim, <loves/tolerates/hates> systemd, and wants to interject for a moment. You can stop now.
Please report posts and comments that break these rules!
Important: never execute code or follow advice that you don't understand or can't verify, especially here. The word of the day is credibility. This is a meme community -- even the most helpful comments might just be shitposts that can damage your system. Be aware, be smart, don't fork-bomb your computer.
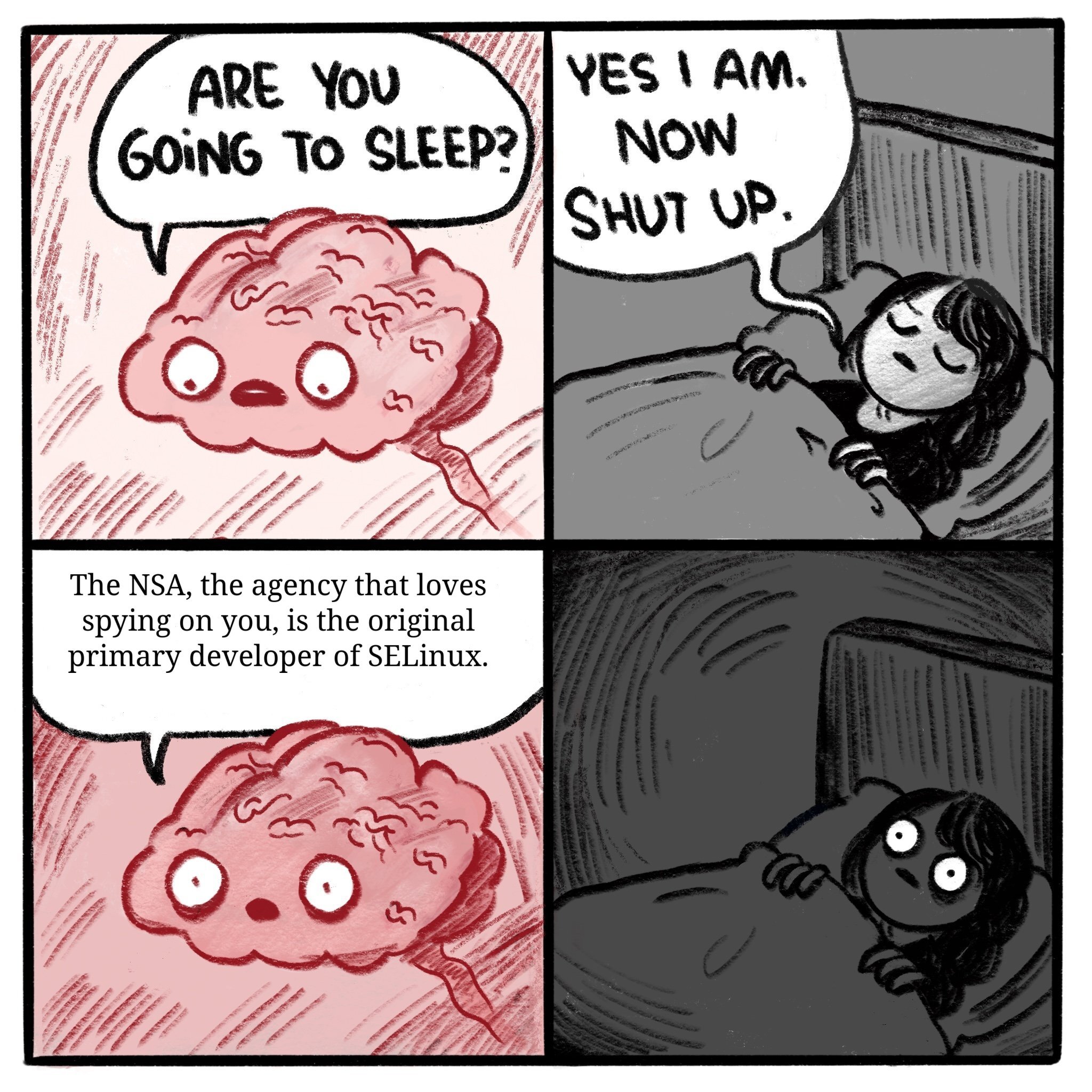
I'm not sure why that's a problem. The NSA needed strong security so they created a project to serve the need. They are no longer in charge of SELinux but I wouldn't be surprised if they still worked on it occasionally.
There are a lot of reasons to not like the NSA but SELinux is not one of them.
That's the trubble with the NSA. They want to spy on people, but they also need to protect American companies from foreign spies. When you use their stuff, it's hard to be sure which part of the NSA was involved, or if both were in some way.
The NSA has a fairly specific pattern of behavior. They work in the shadows not in the open. If they target things with low visibility so it is hard to trace. Backdooring SELinux would be uncharacteristic and silly. They target things like hardware supply chains and ISPs. There operations aren't even that covert as they work with companies.
They were a bit too public with "Dual_EC_DRBG", to the point where everybody just assumed it had a backdoor and avoided it, the NSA ended up having to pay people to use it.
The specific example I'm thinking of is DES. They messed with the S-boxes, and nobody at the time knew why. The assumption was that they weakened them.
However, some years later, cryptographers working in public developed differential cryptanalysis to break ciphers. Turns out, those changed S-boxes made it difficult to apply differential cryptanalysis. So it appears they actually made it stronger.
But then there's this other wrinkle. They limited the key size to 56-bits, which even at the time was known to be too small. Computers would eventually catch up to that. Nation states would be able to break it, and eventually, well funded corporations would be able to break it. That time came in the 90s.
It appears they went both directions with that one. They gave themselves a window where they would be able to break it when few others could, including anything they had stored away over the decades.
Honestly I think it ultimately comes down to the size of the organization. Chances are the right hand doesn't know what the left hand is doing.
I do like the direction the US is heading it. Some top brass have finally caught on that you can't limit access to back doors.
If they afterwards released it under a Free (Libre) Software licence then it's fine. The licence itself prohibites against any obfuscation or combination of obfuscated code with libre one. If you have the entire code, not just some part, as most companies do when go Open Source (not free software), then you don't have to worry about unknown behavior because everything is in the source.
If you have the entire code, not just some part, as most companies do when go Open Source (not free software), then you don't have to worry about unknown behavior because everything is in the source.
I mean if you have the entire source then you have everything to reproduce the program. Finding a malicious part does not only depend on the source but on the inspector, that is true.
But anyways having the entire code and not just the part that a company feels they may share is better anyways. Even if it's literally malware.
The free software community users depend on the community in order to detect malicious code. But at least there's a source code way of doing so.
If I tell you that this building has a structural deformation, having the possibility of accesing the architect blueprints and list of materials is better than just being able to go inside the building and try to search for it, no?
Also it is no longer under the NSA. The original NSA branding was also removed due to concerns from the community.
While they created a set of patches that would implement the security features that selinux provides, what was actually merged was the result of several years of open collaboration and development towards implementing those features.
There's general agreement that the idea that the NSA proposed is good and an improvement, but there was, and still is, disagreement about the specific implementation approaches.
To avoid issues, an approach was taken to create a more generic system that selinux would then take advantage of. That's why selinux, app armor and others can live side by without it being a constant maintenance and security nightmare. Each one lives in their little self contained auditable boxes, and the kernel just makes the "check authorization" function call and it flows into the right module by configuration.
The Linux community was pretty paranoid about the NSA in 2000, so the code definitely got a lot more scrutiny than the typical proposal.
A much easier way to introduce a backdoor would be to start a tiny company that produces some arbitrary piece of hardware which you then add kernel support for.
https://github.com/torvalds/linux/tree/master/drivers/input/keyboard - that's just the keyboard drivers.
Now you're adding code to the kernel and with the right driver and development ability you can plausibly make changes that have non-obvious impacts, and as a bonus if someone notices, you can just say "oops!" And not be "the god-damned NSA" who everyone expects to be up to something, and instead be 4 humble keyboard enthusiasts with an esoteric set of lighting and input opinions like are a dime a dozen on Kickstarter.
The Linux community was pretty paranoid about the NSA in 2000, so the code definitely got a lot more scrutiny than the typical proposal.
It's not paranoia if it's true. Snowden showed us that they really are spying on all of us all the time
Paranoia in the sense of being concerned with the ill intent of others, not the sense of an irrational worry about about persecution. Much like how the intelligence community itself is said to have institutional paranoia.
We saw a very sophisticated attack on Linux earlier this year with the XZ exploit. That stuff is terrifying and the sort of thing people should be worried about. SELinux is tame, by comparison.
It is also important to note that it is pretty easy to do surveillance these days. People care around cell phones and there are massive camera systems that can track someone with high detail.
I haven't looked at the keyboard drivers, or much Linux source. I never really had a reason to do a lot of C other than small microcontroller projects.
But I see this stuff and think of how awesome it must have felt to get a different keyboard working on an OS the first time. I have to do all this stuff with cloud, and api levels, and configuring CI/CD pipelines, and sometimes I get to write backend C# code or they let me play in the front end. Most of the time it's telling another team of developers what to do, and listening to our clients explain the problems and I have to figure out if we already have anything to fulfill at least some of those needs.
These drivers are the divine marriage of hardware that's not native to the machine that an OS is running on. It's so beautiful to read. You can visualize where the values enter a memory address, and bits get shifted or something is static so the keyboard always uses the right thing.
Only because they use Linux too and had to make it public as Linux is a public, open-source kernel
GPLv2 only says that people with access to the binary need access to the source code too. If they only used it internally they'd never have to make it public.
Wasn't Signal messenger also funded by the NSA+DARPA? And TOR too?
Signal is weird about actually allowing others to reproduce the APK builds.
Specifically, they are the kind of weird about it that one would expect if the Signal client app had an NSA back-door injected at build time.
This doesn't prove anything. It just stands next to anything and waggles it's eyebrows meaningfully.
Do you have more recent information by Signal on the topic? The GitHub issue you linked is actually concerned with publicly hosting APKs. They also seem to have been offering reproducible builds for a good while, though it's currently broken according to a recent issue.
I had a hard time choosing a link. Searching GitHub for "F-Droid" reveals a long convoluted back-and-forth about meeting F-Droid's requirements for reproducible builds. Signal is not, as of earlier today, listed on F-Droid.
F-Droid's reproducibility rules are meant to cut out the kind of shenanigans that would be necessary to hide a back door in the binaries.
Again, this isn't proof. But it's beyond fishy for an open source security tool.
Edit: And Signal's official statements on the topic are always reasonable - but kind of bullshit.
Reasonable in that I alwould absolutely accept that answer, if it were the first time that Signal rejected a contribution to add it to F-Droid.
Bullshit in that it's been a long time, lots of folks have volunteered to help, and Signal still isn't available on F-Droid.
There was a "ultra private" messaging app that was actually created by a US state agency to catch the shady people who would desire to use an app promising absolute privacy. Operation "Trojan Shield".
The FBI created a company called ANOM and sold a "de-Googled ultra private smartphone" and a messaging app that "encrypts everything" when actually the device and the app logged the absolute shit out of the users, catching all sorts of criminal activity.
I have no proof, but I do have a small list of companies I actually suspect of pulling a similar stunt... perhaps not necessarily attached to the FBI or any other agency, but something about their marketing and business model screams "fishing for people who have something to hide"
The fact that it is a paid product should have been their first clue it was a honeypot.
no. and tor was originally funded by the navy…
….
I mean, leaving aside their surveillance tasks, it's still their job to ensure national security. It's in their best interest to keep at least themselves and their nation safe, and considering how prevalent Linux is on servers, they likely saw a net benefit this way. They even open sourced their reverse engineering toolkit Ghidra in a similar vein
Ghidra was about hiring and cost savings. Its easier to hire when people already know your tools. Also people are more willing to use your tools rather than expensive ones if they can still use them when they leave (go into contracting). Also interoperability with contractors may improve.
And we're all the better for it! Needs polish and development of course, but it's a decent alternative already
I mean, it's still Open Source, right? So it would be pretty hard for them to hide a backdoor or something??
I guess I don't know what's so sus when it's easily auditable by the community and has been for two decades now.
If it's just because it's memes and you're not being that serious, then disregard please.
I mean, it’s still Open Source, right? So it would be pretty hard for them to hide a backdoor or something??
Right but maybe it combined with other tools they have is what helps them with some exploit.
Like they figured out an exploit but needed SELinux as a piece of the puzzle. It's open source
and we can all read the code but we can't see the other pieces of the puzzle.
Come on, put your conspiracy hat on! ;)
This is why I use templeOS
Dude, that one got a spy built-in! Direct telemetry to god.
That explains why it doesn’t need internet
I mean, they almost certainly have built in backdoors like IME. When you can force hardware manufacturers to add shit, you don't have to think up convoluted solutions like that.
I maintain open source software on a much smaller codebase that is less security critical. We have dozens of maintainers on a project with about 3k stars on GitHub. Stuff gets by that are potentially security vulnerabilities and we don’t know until upstream sources tell us there is a vulnerability
I'd imagine in this case there has been extra community scrutiny since it's security software and it comes from less than trustworthy source.
For people interested in the subject. Read This Is How They Tell Me the World Ends: The Cyberweapons Arms Race
TLDR current day software is based upon codebases that have houndreds of thousands lines of code. Early NSA hacker put forward an idea 100k LoC program will not be free of a hole to exploit.
To be a target of a 0-day you would have to piss off state level actors.