this post was submitted on 15 Apr 2024
657 points (95.3% liked)
linuxmemes
21611 readers
1338 users here now
Hint: :q!
Sister communities:
Community rules (click to expand)
1. Follow the site-wide rules
- Instance-wide TOS: https://legal.lemmy.world/tos/
- Lemmy code of conduct: https://join-lemmy.org/docs/code_of_conduct.html
2. Be civil
- Understand the difference between a joke and an insult.
- Do not harrass or attack members of the community for any reason.
- Leave remarks of "peasantry" to the PCMR community. If you dislike an OS/service/application, attack the thing you dislike, not the individuals who use it. Some people may not have a choice.
- Bigotry will not be tolerated.
- These rules are somewhat loosened when the subject is a public figure. Still, do not attack their person or incite harrassment.
3. Post Linux-related content
- Including Unix and BSD.
- Non-Linux content is acceptable as long as it makes a reference to Linux. For example, the poorly made mockery of
sudoin Windows. - No porn. Even if you watch it on a Linux machine.
4. No recent reposts
- Everybody uses Arch btw, can't quit Vim, and wants to interject for a moment. You can stop now.
Please report posts and comments that break these rules!
Important: never execute code or follow advice that you don't understand or can't verify, especially here. The word of the day is credibility. This is a meme community -- even the most helpful comments might just be shitposts that can damage your system. Be aware, be smart, don't fork-bomb your computer.
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
There's always a risk of JavaScript breaking out of the sandbox and crap like that. Browser vendors do their best to protect against things like that but security is often a trade-off for speed and people like fast software, not to mention browsers are huge and complex and they're going to have vulnerabilities. A browser's whole job is to execute remote untrusted code, do you trust it that much to be flawless?
...... I mean, I don't but I use it anyway so ¯\_(ツ)_/¯
Linux security noob here but can't you just run the browser in a chroot with everything isolated?
Yeah, that should work too... but you don't get to see any of your local files...
Made a Nix library for this. For a simple setup you can just build this (untested) and run the result:
It doesn't have user isolation yet, so if it escapes the browser and the chroot (which doesn't have a
/procunless you setproc = /proc;, and runs in a PID namespace either way) your files are still at risk. However, this is still pretty secure, and you can run the script itself as a different user (it creates a new UID namespace so chrooting can be done without root).I mean, yeah, sure. But at this point, if that’s really a worry, one should not trust any sandbox. OSes are huge and complex and will have vulnerabilities too. Hell, there could be a xz level backdoor currently in the wild and nobody knows any better lol
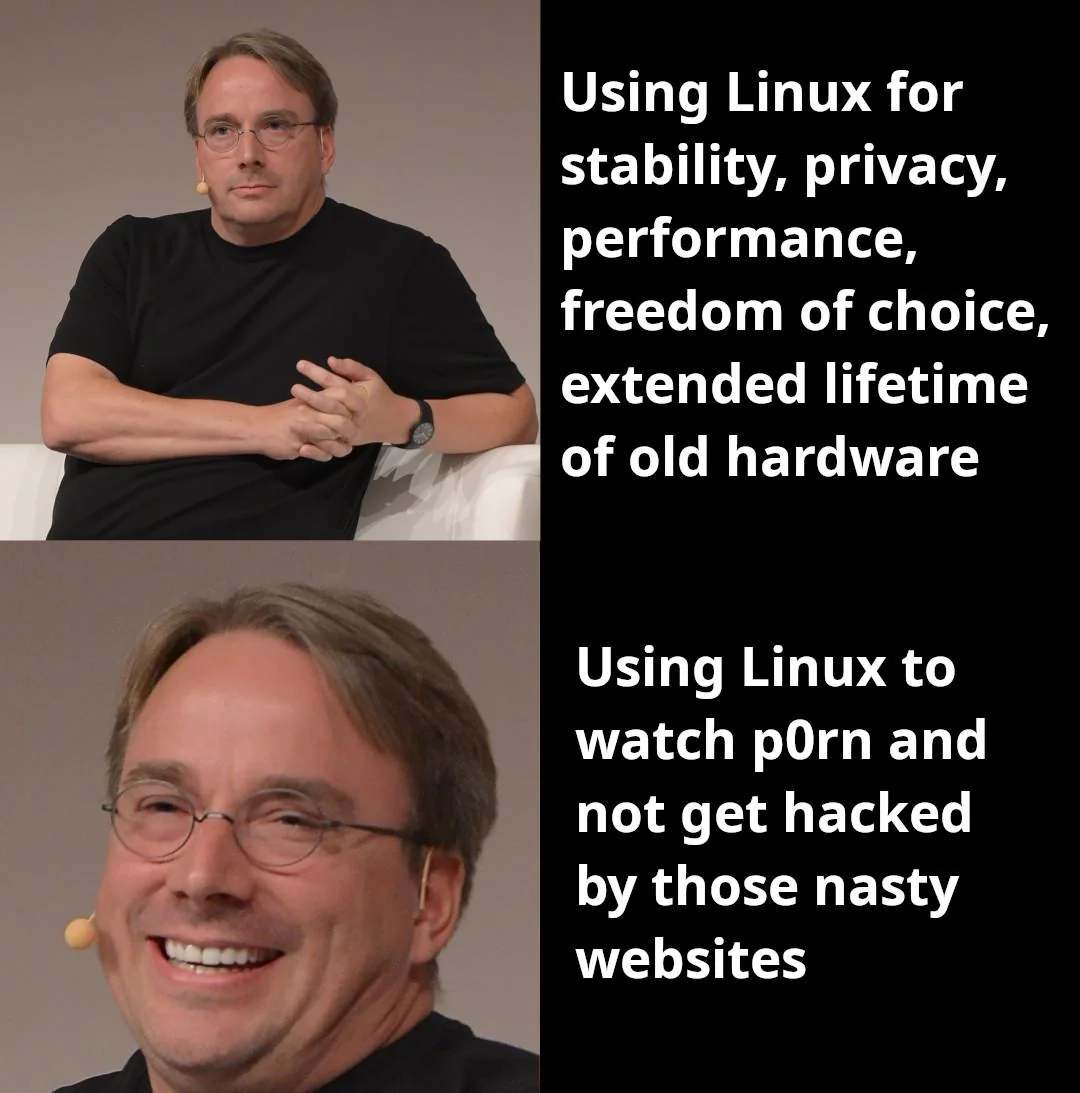
Right, that's where OP comes in - most malware will be made for Windows, so if you visit such a malicious website, it'll likely be inert under Linux!
.... I'm not saying this is a great reason to use Linux, but there's at least a little bit of merit to it.