this post was submitted on 02 Nov 2023
541 points (98.9% liked)
Programmer Humor
32396 readers
499 users here now
Post funny things about programming here! (Or just rant about your favourite programming language.)
Rules:
- Posts must be relevant to programming, programmers, or computer science.
- No NSFW content.
- Jokes must be in good taste. No hate speech, bigotry, etc.
founded 5 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
[This comment has been deleted by an automated system]
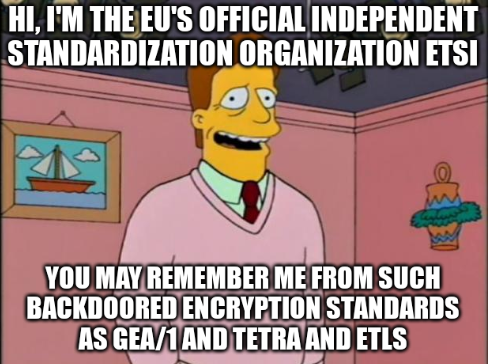
The new proposal demands browsers automatically trust government created root certificates. That means any EU government can do a man-in-the-middle attack on any end user running that web browser, even users in other countries. There is no reason to do that other than to spy on people or to manipulate the content that they're viewing.
If any government, or company for that matter, wants to make their own root cert and deploy it to all their users/machines they can already do that easily. A lot of companies that work with sensitive data already do this, and some companies (ex: symantec) provide solutions to do it very easily, so the IT team can see everything the users are doing.
https://spectrum.ieee.org/diginotar-certificate-authority-breach-crashes-egovernment-in-the-netherlands
This is probably the seed of this madness
Right... uh. Listen, my government used a local/regional CA. Do you want to know what happened? My government got the privilege to emergency re-issue all of their TLS certificates with a different CA because the local/regional CA forgot to renew its own CA certificate. Everything was down. Government websites, government services, eID SSO authentication, etc. You had one job!