this post was submitted on 16 Oct 2023
1760 points (99.3% liked)
internet funeral
7551 readers
1 users here now
ㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤart of the internet
What is this place?
• !hmmm@lemmy.world with text and titles
• post obscure and surreal art with text
• nothing memetic, nothing boring
• unique textural art images
• Post only images or gifs (except for meta posts)
Guidlines
• no video posts are allowed
• No memes. Not even surreal ones. Post your memes on !surrealmemes@sh.itjust.works instead
• If your submission can be posted to !hmmm@lemmy.world (I.e. no text images), It should be posted there instead
This is a curated magazine. Post anything and everything. It will either stay up or be lost into the void.
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
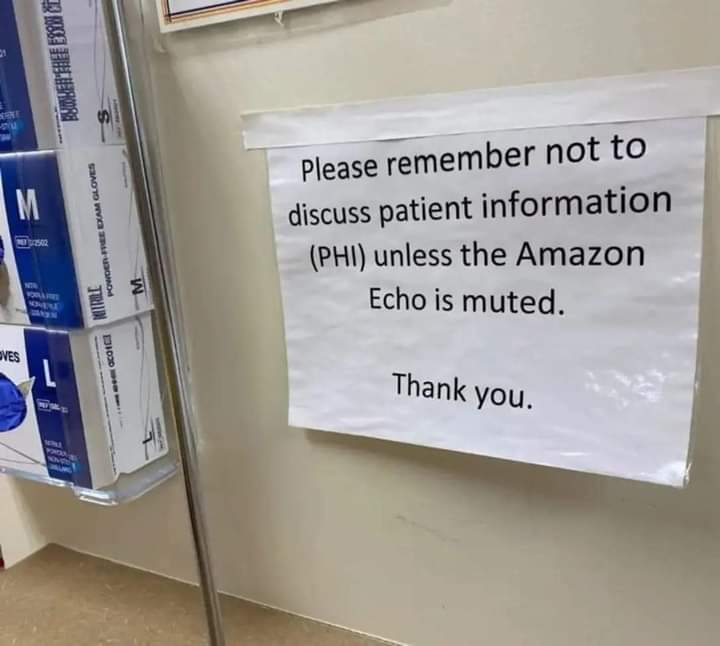
You're all missing the real kicker here - this sign is only here for the HIPAA auditor. Everyone knows that no one is actually going to mute the thing.
We're not all like that. Some of us do really care (a whole lot) about the person, and not just "the patient". We get eye-rolled and sighed at sometimes because we speak up; but it doesn't matter because advocating for our patients is one of our top priorities.
Some hospitals have better work-cultures than others, but all of them have at least a few who truly give a damn
I would like to thank you for maintaining integrity when it is not easy. I know it can be frustrating.
That's cool, but given the majority of the population literally has zero clue on what privacy actually is, or what tech is intentionally doing to destroy it, it's a lost cause. The healthcare system is one of the worst places for any personal information.
Also muting it probably doesn't stop it listening, it just stops its response.
No, there is a button to make the Echo stop listening.
If you want to prove me wrong, it should be incredibly easy to press the button and record the Echos network activity. If you're right you'd still see network traffic. But nobody has been able to show this so far. I wonder why?
Yeah I read the other comments after making mine. However everyone keeps calling it a "physical" button, and I don't think that's accurate. It won't be a physical switch that opens a circuit, it will be a button that operates a transistor that opens the circuit.
Still, I see no good reason to trust the device - especially in a medical setting.
There's not much difference between a direct switch and a transistor, both will cut the signal and neither is over rideable by software
This is disingenuous at best and incorrect at worst. The mute button on the Echo is just that, a button; it is not a switch. It is software-controlled and pushing it just sends a signal to the microcontroller to take some action. For instance, one action is to turn on the red indicator light; that's definitely not physically connected to the mute button.
Maybe another response of pushing the button is to disable the transistor used for the microphone, but it's more likely that it just sets a software flag for the algorithm to stop its processing of the microphone input signal. Regardless of which method it uses, the microcontroller could undoubtedly just decide to revert that and listen in, either disabling or not disabling the red light at the same time.
But I personally don't think it listens in when muted. I don't think it spies on us to target ads based on what we say around it. I'm not worried that the mic mute function doesn't work as intended.
But I fully understand that it is fully capable of it, technically speaking.
I don't know the internal workings of the echo, I was responding to a comment that said it "operates a transistor". Which is way different than it being an input to a microcontroller.
If the button is just connected to a transistor, it's not software controllable, since transistors are electronical devices that don't interpret any software. A microcontroller does execute software. There's a big difference.
A transistor is controlled by software so yes, it's absolutely over rideable.
Transistors are simple electronical devices. They don't run software. You can control their inputs with another device (such a microcontroller) that does run software. You can also control their inputs with a button. You can't control their output with software.
I don't know how an Amazon echo is wired up, but if you just have a button connected to the gate of the transistor, it works basically the same as a mechanical switch.
If the Echo stored the audio and then sent it sometime after you unmute, it would still pass your test.
Which you could easily see by looking at the amount of traffic sent after unmuting, unless you believe that Amazon secretly found an infinite compression algorithm they use only in muted Echo devices.
Unless some or all of it was sent along during the next time you actually do a voice command.
Tbf to foobar, that should still give a falsifiable and testable data-difference if you are willing to alter your behaviour around experimentation for an extended period of time
Though, there are always more ways to hide traffic
Again: Which you could easily see by looking at the amount of traffic sent after unmuting, unless you believe that Amazon secretly found an infinite compression algorithm they use only in muted Echo devices.
You understand that sending more information means more traffic? Unless - as I stated - they found a perfect compression algorithm, you'd be able to tell.
I’m a little confused as to why you are being so condescending. Every time you say “this is so simple if you do X”. And then I say “what about Y?” And then you’re like “that’s obvious too, just do Z” and kind of insulting me, even though you did not account for it in your prior comment. And it becomes less trivial with each additional test.
Your first method involves simply checking if there is any traffic after muting. Your revised method involves additionally checking if there is any traffic for some period of time after muting (how long?). And now your third method involves doing the first two things as well as gathering data on the average amount of traffic in your requests generally and deciding whether subsequent traffic during requests after muting for an unspecified amount of time is significantly large enough to conclude it is sending information acquired during muting.
But if they send it a little bit at a time, or they just leak a small portion of it occasionally in some requests, I think it would be very challenging to conclude definitively one way or the other.
I’m actually aware that there is no infinite compression algorithm, so you don’t need to keep saying that. And to be honest it just makes you look like you are lacking imagination because it’s not the only way to make detection difficult as illustrated by my responses.
I'm not sure that's the case. We have one at work and if it thinks you're calling out to it repeatedly it will say out loud that its mic is off and that you have to enable it.
It might just be the part that listens for "Alexa" but that audio buffer is available to the device and it can do things with it.
This is the funniest thing I've read today (though I'm not sure if it is a joke).
I just tried it with mine, it doesn't react in any way.